In order to obtain a security guard license in new york state unarmed you must complete the following steps.
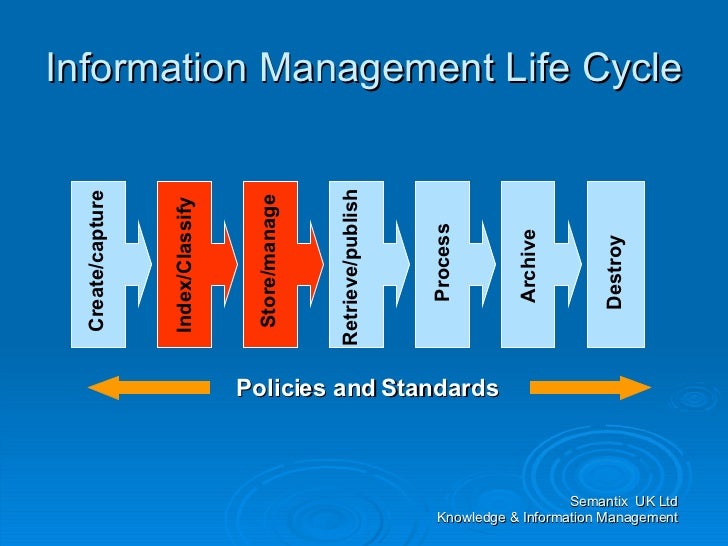
Steps of the information security program lifecycle classification.
Dod military civilian and contractor personnel with a functional knowledge of the dod information security program.
This manual is composed of several volumes each containing its own purpose.
Classification safeguarding dissemination declassification and destruction.
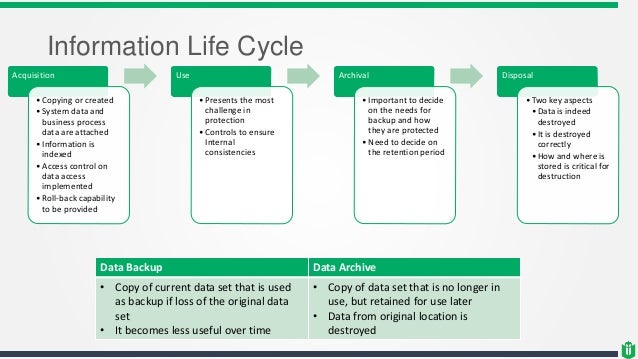
At vala secure we use a lifecycle model that serves as a useful baseline to help build a solid foundation for any security program across any type of organization and industry focus.
See enclosure 1.
Classification safeguarding dissemination declassification and destruction the unauthorized disclosure of confidential information could reasonably be expected to cause to our national security.
Overview classification and declassification.
It is important to understand that a security program has a continuous life cycle that should be constantly.
Classification safeguarding dissemination declassification and destruction.
Provide an understanding of security classification and declassification guidance to personnel performing classification and declassification actions audience.
Welcome to the security classification guidance course.
Dod information security program.
Using the lifecycle model can provide you with a road map to ensure that your information security is continually being improved.
It covers the information security program lifecycle which includes who what how when and why information such as a document like me is classified known as classification protected known as safeguarding shared known as dissemination downgraded declassified and.
The purpose of the overall manual as authorized by dod directive dodd 5143 01 reference.